���@�r�g
2009-2-20
����ժҪ
ԓ�ӱ���ʹ��“VC”���������x�������c���ӷ���ܛ���ԄӲ��@������“WinUpack”�Ӛ���ʽ����D��������a���裬�Ӛ����L�Ȟ�“26,856 �ֹ�(ji��)”���D�˞�“ ”�������Uչ����“exe”����Ҫͨ�^“�W(w��ng)퓒��R”��“�ļ�����”��“���d�����d”��“�ƄӴ惦���|(zh��)”�ȷ�ʽ������������ҪĿ�Ğ����d��������ľ�R���Ñ����C�\�С�
”�������Uչ����“exe”����Ҫͨ�^“�W(w��ng)퓒��R”��“�ļ�����”��“���d�����d”��“�ƄӴ惦���|(zh��)”�ȷ�ʽ������������ҪĿ�Ğ����d��������ľ�R���Ñ����C�\�С�
�Ñ��ж����l(f��)�F(xi��n)ϵ�y(t��ng)�\�м��W(w��ng)�j(lu��)푑�(y��ng)�������o���M��ϵ�y(t��ng)��ȫģʽ��������ȫܛ���o�������\�У������شűP��Ŀ��c���ƄӴűP�l(f��)�F(xi��n)Autorun.ini�cZTZ.PIF�ļ���
��Ⱦ����
Windows 2000/Windows XP/Windows 2003
����;��
�W(w��ng)퓒��R���ļ����������d�����d���ƄӴ惦���|(zh��)
������ʩ
�Ѱ��bʹ���c���ӷ���ܛ�����Ñ����o��κ��O(sh��)�ã��c���ӷ������Ԅӱ��o����ϵ�y(t��ng)����ԓ���������ֺ��Ɖġ��oՓ���Ƿ��ѽ�(j��ng)���������°汾���c���ӷ������܉���Ч���ԓ������������]�Ќ��c���ӷ���ܛ�����������°棬�c���ӷ���ܛ���ڰl(f��)�F(xi��n)ԓ��������ʾ���l(f��)�F(xi��n)“δ֪ľ�R”��Ոֱ���x��h��̎������D1����
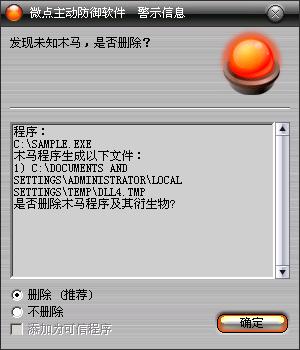
�D1 �c���ӷ���ܛ���ԄӲ��@δ֪������δ������
������ѽ�(j��ng)���c���ӷ���ܛ�����������°汾���c������ʾ���l(f��)�F(xi��n)"Worm.Win32.AutoRun.kqk”��Ոֱ���x��h������D2����
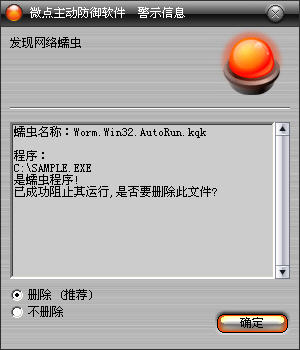
�D2 �c���ӷ���ܛ��������ث@��֪����
����δʹ���c���ӷ���ܛ�����Ñ����c���������ҽ��h��
1����Ҫ�ڲ���վ�c���d�ǹٷ��汾��ܛ���M�а��b�����ⲡ��ͨ�^�����ķ�ʽ�M������ϵ�y(t��ng)��
2�����h�P(gu��n)�]U�P�ԄӲ��ţ����w�������E���_ʼ->�\��->gpedit.msc->Ӌ��C����->����ģ��->ϵ�y(t��ng)->���҂�(c��)�ҵ�"�P(gu��n)�]�ԄӲ���"->�p��->�x��"�ц���"��
3���M�쌢���Ě���ܛ�����������������°汾�M�в隢�����_���������r�ؾW(w��ng)�j(lu��)�����L��������Ȼ�Ю�����rՈע�⼰�r�c���I(y��)�İ�ȫܛ���S��(li��n)ϵ�@ȡ���g(sh��)֧�֡�
4���_��windows�ԄӸ��£����r���©���a����
δ���b�c���ӷ���ܛ�����քӽ�Q�k����
1���քӄh�������ļ���
����%SystemRoot%\system32\dllcache\linkinfo.dll
����%SystemRoot%\system32\sbbsk.ini,
����%Program Files%\bccd.pif
2���քӄh������ע�Ա�ֵ��
�����I��HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options
����ֵ��ȫ��
�����I��HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\naks
�����I��HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\fangdapp
3��������ע�Ա���Ğ�����ֵ��
�����I��HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced\Folder\Hidden\SHOWALL
����ֵ��CheckedValue
������(sh��)��(j��)��1
�����I��HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager
����ֵ��PendingFileRenameOperations
������(sh��)��(j��)����
3���ޏͰ�ȫģʽ��
׃������
%SystemDriver%������������������ϵ�y(t��ng)���ڷօ^(q��)��ͨ����“C:\”
%SystemRoot%��������������������WINDODWS����Ŀ䛣�ͨ����“C:\Windows”
%Documents and Settings%���������Ñ��ęnĿ䛣�ͨ����“C:\Documents and Settings”
%Temp%���������������������������R�r�ļ��A��ͨ����“C:\Documents and Settings\��ǰ�Ñ����Q\Local Settings\Temp”
%ProgramFiles%������������������ϵ�y(t��ng)����Ĭ�J���bĿ䛣�ͨ���飺“C:\ProgramFiles”
��������
��1������Ո��(n��i)����g�����Ӿ��̣�ע��CMD.exe������CMD.exe���d�ӑB(t��i)�죻
��2����ע��rundll32.exe������rundll32.exe���d�ӑB(t��i)�죻
��3�����Lԇ�P(gu��n)�]���ȫܛ����
��4������ע�Ա���ӳ��ٳָ��ȫܛ������ָ��“%SystemRoot%\system32\dllcache\spoolsv.exe”��
��5������ע�Ա����Ɖ�ϵ�y(t��ng)��ȫģʽ��
��6������ע�Ա����h����Ҋ��ȫܛ������헣�
��7����ጷ��(q��)�ӣ��֏�SSDT����
��8����ע��net1.exe������net1.exe�z�y����(w��)��
��9����ע��sc.exe������sc.exe�h�����ְ�ȫܛ������(w��)��
��10�����O(sh��)��Autorun.ini�������شűP�c���ƄӴűP��
��11�����B�ӾW(w��ng)�j(lu��)�����d���������ļ�����(zh��)�У�
��12�������d�����б����xȡ�����d��������(zh��)�У�
����
����������(chu��ng)���ļ���
����
����%Program Files%\avpp.pif
����%SystemDriver%\Runt.dll
����%SystemRoot%\system32\dllcache\linkinfo.dll
����%SystemRoot%\Fonts\fangdapp.sys
����%SystemRoot%\system32\sbbsk.ini,
����%Program Files%\bccd.pif
����%SystemRoot%\Fonts\naks.sys
����
�����ڱ��شűP�Ϳ��ƄӴűP��Ŀ����������ļ���
����AUTORUN.INF
����ZTZ.PIF
����
����
�����������ļ���
����
����%SystemRoot%\system32\mfc71.dll
����
���������h���ļ���
����
����%Program Files%\avpp.pif
����%SystemDriver%\Runt.dll
����%SystemRoot%\Fonts\fangdapp.sys
����%SystemRoot%\Fonts\naks.sys
����
����������(chu��ng)��ע�Ա���
����
����HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\naks
����HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\fangdapp
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360rpt.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360safe.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360safebox.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360tray.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ANTIARP.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ArSwp.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Ast.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AutoRun.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AutoRunKiller.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AvMonitor.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AVP.com
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AVP.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\CCenter.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Frameworkservice.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\GFUpd.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\GuardField.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\HijackThis.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\IceSword.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Iparmor.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KASARP.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\kav32.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KAVPFW.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\kavstart.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\kissvc.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\kmailmon.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KPfwSvc.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KRegEx.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KVMonxp.kxp
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KVSrvXP.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KVWSC.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\kwatch.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Mmsk.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Navapsvc.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\nod32krn.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Nod32kui.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\PFW.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\QQDoctor.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RAV.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavMon.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavMonD.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Ravservice.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavStub.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavTask.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RAVTRAY.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Regedit.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rfwmain.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rfwProxy.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rfwsrv.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Rfwstub.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RsAgent.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Rsaupd.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RsMain.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rsnetsvr.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RSTray.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Runiep.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\safeboxTray.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ScanFrm.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SREngLdr.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\TrojanDetector.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Trojanwall.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\TrojDie.kxp
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\VPC32.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\VPTRAY.exe
����HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\WOPTILITIES.exe
����
����������ע�Ա���
����
�����I��HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager
����ֵ��PendingFileRenameOperations
������(sh��)��(j��)��\??\C:\Sample.exe
�����I��HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced\Folder\Hidden\SHOWALL
����ֵ��CheckedValue
������(sh��)��(j��)��2
����
���������h��ע�Ա���
����
����HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\{4D36E967-E325-11CE-BFC1-08002BE10318}
����HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Network\{4D36E967-E325-11CE-BFC1-08002BE10318}
����HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\360Safetray
����HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\360Safebox
����HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\KavStart
����HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\vptray
����HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ccApp
����HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\RavTray
����
����������(chu��ng)���M�̣�
����
����%Program Files%\avpp.pif
����
���������L���W(w��ng)�j(lu��)��
����
����http://m.w**8.com/dd/x.gif
����http://m.w**8.com/tt.txt
����http://d.w**8.com/dd/1.exe
����http://d.w**8.com/dd/2.exe
����http://d.w**8.com/dd/6.exe
����http://d.w**8.com/dd/9.exe
����http://d.w**8.com/dd/10.exe
