ľ�R���d��
Trojan-Downloader.Win32.AntiAV.f
���@�r(sh��)�g
2010-8-24
Σ���ȼ�(j��)
��
�����Y��
ԓ�ӱ���ʹ��“C”������ľ�R�������c(di��n)����(d��ng)����ܛ���Ԅ�(d��ng)���@������“UPack”�Ӛ���ʽԇ�D��������a����,�Ӛ����L(zh��ng)�Ȟ�“30,617”�ֹ�(ji��)���D��(bi��o)��“ ”�������U(ku��)չ����“exe”����Ҫͨ�^(gu��)“�ļ�����”��“���d�����d”��“�W(w��ng)�(y��)���R”�ȷ�ʽ������������ҪĿ�������d�����������\(y��n)�С�
”�������U(ku��)չ����“exe”����Ҫͨ�^(gu��)“�ļ�����”��“���d�����d”��“�W(w��ng)�(y��)���R”�ȷ�ʽ������������ҪĿ�������d�����������\(y��n)�С�
�����Ñ��ж���(hu��)���F(xi��n)�W(w��ng)�j(lu��)����������ܛ���o(w��)���˳���ʧЧ�����F(xi��n)����δ֪�M(j��n)�̡�Windowsϵ�y(t��ng)�\(y��n)�о����͟o(w��)�ʈ�(b��o)�e(cu��)�ȬF(xi��n)��
��Ⱦ��(du��)��
Windows 2000/Windows XP/Windows 2003/Windows Vista/ Windows 7
����;��
�ļ��������W(w��ng)�(y��)���R�����d�����d
������ʩ
�Ѱ��bʹ���c(di��n)����(d��ng)����ܛ�����Ñ����o(w��)��κ��O(sh��)�ã��c(di��n)����(d��ng)�������Ԅ�(d��ng)���o(h��)����ϵ�y(t��ng)����ԓ���������ֺ��Ɖġ��o(w��)Փ���Ƿ��ѽ�(j��ng)����(j��)�����°汾���c(di��n)����(d��ng)�������܉���Ч���ԓ������������](m��i)�Ќ��c(di��n)����(d��ng)����ܛ������(j��)�����°棬�c(di��n)����(d��ng)����ܛ���ڰl(f��)�F(xi��n)ԓ������(b��o)����ʾ���l(f��)�F(xi��n)“δ֪ľ�R”��Ո(q��ng)ֱ���x��h��̎������D1��
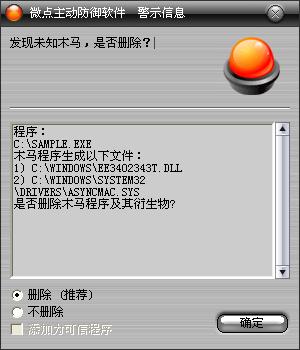
�D1 �c(di��n)����(d��ng)����ܛ���Ԅ�(d��ng)���@δ֪������δ����(j��)��
������ѽ�(j��ng)���c(di��n)����(d��ng)����ܛ������(j��)�����°汾���c(di��n)����(b��o)����ʾ���l(f��)�F(xi��n)ľ�R"Trojan-Downloader.Win32.AntiAV.f”��Ո(q��ng)ֱ���x��h������D2����
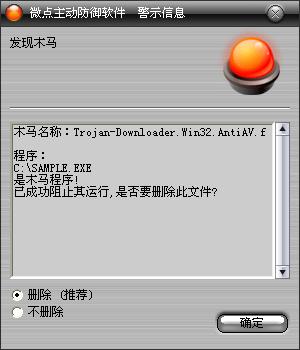
�D2 �c(di��n)����(d��ng)����ܛ������(j��)��ث@��֪����
δ���b�c(di��n)����(d��ng)����ܛ�����ք�(d��ng)��Q�k����
1����ؐ��ͬ�汾�������ļ���Q���±����ļ���
%SystemRoot%\system32\drivers\etc\hosts
%SystemRoot%\system32\userinit.exe
2���ք�(d��ng)�h�������ļ���
%SystemRoot%\system32\scvhost.exe
X:\recycle.{645FF040-5081-101B-9F08-00AA002F954E}\kav32.exe��X��űP�P����
X:\AUTORUN.INF��X��űP�P����
%SystemRoot%\extext11607390t.exe���S�C(j��)������
3���ք�(d��ng)�h��ע��(c��)���(xi��ng)��
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
���Q��RsTray
��(sh��)��(j��)��C:\WINDOWS\system32\scvhost.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\
������ӳ��ٳ�
׃������
%SystemDriver%��������������ϵ�y(t��ng)���ڷօ^(q��)��ͨ����“C:\”
%SystemRoot%����������������WINDODWS����Ŀ䛣�ͨ����“C:\Windows”
%Documents and Settings%�����Ñ��ęnĿ䛣�ͨ����“C:\Documents and Settings”
%Temp%�����������������������R�r(sh��)�ļ��A��ͨ����“C:\Documents and Settings\��(d��ng)ǰ�Ñ����Q\Local Settings\Temp”
%ProgramFiles%��������������ϵ�y(t��ng)����Ĭ�J(r��n)���bĿ䛣�ͨ���飺“C:\ProgramFiles”
��������
(1) �������_(k��i)ӛ�±��������䴰�ڡ������ڄt�l(f��)���P(gu��n)�]����Դ˙z�(y��n)ϵ�y(t��ng)�\(y��n)�Эh(hu��n)���Ƿ�������
(2) �{(di��o)�������У�����ESET NOD32�ķ���(w��)�(xi��ng)�����Y(ji��)�����P(gu��n)�M(j��n)�̣�
“cmd /c sc config ekrn start= disabled”
“cmd.exe /c taskkill.exe /im ekrn.exe /f”
“cmd.exe /c taskkill.exe /im egui.exe /f”
(3) �@ȡϵ�y(t��ng)·������(chu��ng)���ļ���%SystemRoot%\ee3402343t.dll���S�C(j��)���������ɹ���(chu��ng)���M(j��n)�̣��{(di��o)��rundll32.exe��testall�酢��(sh��)��(l��i)���dԓ��(d��ng)�B(t��i)朽ӎ�(k��)�ļ���
(4) %SystemRoot%\ee3402343t.dll�@ȡ���������(qu��n)����Ϣ�����������(qu��n)��������SeDebugPrivilege��(qu��n)�ޡ�
(5) �{(di��o)��sfc_os.dll��(k��)�е���̖(h��o)����(sh��)�����Windowsϵ�y(t��ng)���o(h��)���ɹ�����Q%SystemRoot%\system32\drivers\·���µ�����ϵ�y(t��ng)�(q��)��(d��ng)�ļ�AsyncMac.sys��aec.sys
(6)%SystemRoot%\system32\drivers\aec.sys�֏�(f��)SSDT��(l��i)�����ȫܛ��������ϵ�y(t��ng)�^�ӡ�%SystemRoot%\system32\drivers\AsyncMac.sys�t�Á�(l��i)���(q��)��(d��ng)�ӽY(ji��)����ȫܛ���M(j��n)�̡�
(7)���Ҵ�����ȫܛ���M(j��n)�̣�һ���l(f��)�F(xi��n)�t�����Y(ji��)������ɺ������в��ҵİ�ȫܛ����ӳ��ٳ֡����ҵİ�ȫܛ���У�“360delays.exe”“KSWebShield.exe”“rssafety.exe”“LiveUpdate360.exe”“MPMon.exe”“MPSVC2.exe”“RegGuide.exe”“rfwsrv.exe”“DrUpdate.exe”“QQDoctorRtp.exe”“KWatch.exe”“Uplive.exe”“KAVStart.exe”“udaterui.exe”“McTray.exe”“SHSTAT.exe”“ccSvcHst.exe”“xcommsvr.exe”“vsserv.exe”“livesrv.exe”“bdagent.exe”“mcinsupd.exe”“mcshell.exe”“Framewor.exe”“kService.exe”“vstskmgr.exe”“mcagent.exe”“mcnasvc.exe”“mcmscsvc.exe”“mcsysmon.exe”“mfevtps.exe”“mcupdmgr.exe”“vptray.exe”“ccapp.exe”“rtvscan.exe”“defwatch.exe”“ccEvtMgr.exe”“ccSetMgr.exe”“KVSrvXP.exe”“KPFW32.exe”“engineserver.exe”“KavStart.exe”“kmailmon.exe”“KPfwSvc.exe”“KISSvc.exe”“MPSVC1.exe”“MPSVC.exe”“MpfSrv.exe”“naPrdMgr.exe”“rsnetsvr.exe”“mcshield.exe”“McProxy.exe”“QQDoctor.exe”“AgentSvr.exe”“RavScanFrm.exe”“RsTray.exe”“RavStub.exe”“CCenter.exe”“RavTask.exe”“RavMonD.exe”“RavMon.exe”“egui.exe”“mfeann.exe”“RsAgent.exe”“ekrn.exe”“antiarp.exe”“360tray.exe”“360Safebox.exe”“safeboxTray.exe”“avp.exe”
��(du��)��(y��ng)��ӳ��ٳ�·���飺
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\
8) �h�������_(k��i)�C(j��)����(d��ng)�(xi��ng)��
(9) ����Դ����ȴ��M(j��n)�̈�(zh��)�У���(zh��)���ꮅ��h��%SystemRoot%\ee3402343t.dll�ļ�
(10)��(chu��ng)�����̣��@ȡ���شűP�P�����鿴�űP���ԣ��l(f��)�F(xi��n)���شűP����Ƅ�(d��ng)�惦(ch��)���t��(chu��ng)���ļ��AX:\recycle.{645FF040-5081-101B-9F08-00AA002F954E}\��X��űP�P���������b�ɻ���վ�����Ԟ�ֻ�xϵ�y(t��ng)�[�ء���ɺ�������kav32.exe�����Q��(f��)�Ƶ�ԓĿ��¡�ͬ�r(sh��)�ڴűP��Ŀ���(chu��ng)��X:\AUTORUN.INF��X��űP�P����, ���Ԟ�ֻ�xϵ�y(t��ng)�[�أ�ʹ���Ñ�һ�����_(k��i)��(du��)��(y��ng)�űP��ϵ�y(t��ng)���(hu��)�Ԅ�(d��ng)�\(y��n)�в�������
(11) �����{(di��o)���������P(gu��n)�]Windows��ȫ�������ĺ�Intemet�B�ӹ����ͷ���������(w��)����(du��)��(y��ng)����飺
“cmd /c net stop wscsvc”
“cmd /c net stop SharedAccess”
“cmd /c sc config sharedaccess start= disabled”
(12) ������(chu��ng)���ļ�%SystemRoot%\extext11607390t.exe���S�C(j��)����������(chu��ng)���ɹ����\(y��n)��ԓ����
(13) extext11607390t.exe��(chu��ng)������“XETTETT......”�Ļ����w�����؏�(f��)�\(y��n)�С����������(qu��n)�ޣ���%SystemRoot%\system32\scvhost.exe�O(sh��)���_(k��i)�C(j��)����(d��ng)�(xi��ng)����(du��)��(y��ng)ע��(c��)��ֵ�飺
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
���Q��RsTray
��(sh��)��(j��)��C:\WINDOWS\system32\scvhost.exe
(14) ��(chu��ng)�����̣���ָ���W(w��ng)ַ���d�ęn��Q%SystemRoot%\system32\drivers\etc\hosts�ļ����������δ�����ȫܛ���W(w��ng)ַ��
(15) ��(chu��ng)�����̣��B�Ӻڿ�ָ���W(w��ng)վ�������Ñ�ϵ�y(t��ng)�汾�W(w��ng)��MAC��ַ����Ϣ�l(f��)�͵�ԓ�W(w��ng)վ��(sh��)��(j��)��(k��)�С�
(16) �L��(w��n)ָ���W(w��ng)ַ�����d�������������\(y��n)�С�
(17) ����Դ����@ȡϵ�y(t��ng)·������(chu��ng)���(q��)��(d��ng)�ļ�%SystemRoot%\system32\drivers\pcidump.sys����ɺ�����d�����(w��)�(xi��ng)����extext11607390t.exe�ĵ�ַ����%SystemRoot%\system32\userinit.exe�ļ��ĵ�ַ���g����Ⱦuserinit.exe�ļ���֮�h��pcidump.sys�͌�(du��)��(y��ng)����(w��)�(xi��ng)
(18) �����������(f��)�ƞ�%SystemRoot%\system32\scvhost.exe
(19) �������Լ�����·����(chu��ng)����̎���ļ�X:\_temp.bat��X�鲡��Դ��������·��������ɺ��\(y��n)��ԓ��̎��h������Դ�������̎��������
������(chu��ng)���ļ���
%SystemRoot%\ee3402343t.dll���S�C(j��)������
%SystemRoot%\system32\drivers\aec.sys
%SystemRoot%\system32\drivers\AsyncMac.sys
X:\recycle.{645FF040-5081-101B-9F08-00AA002F954E}\kav32.exe��X��űP�P����
X:\AUTORUN.INF��X��űP�P����
%SystemRoot%\extext11607390t.exe���S�C(j��)������
%SystemRoot%\system32\drivers\etc\hosts
%SystemRoot%\system32\drivers\pcidump.sys
%SystemRoot%\system32\scvhost.exe
X:\_temp.bat��X�鲡��Դ��������·����
�����h���ļ���
%SystemRoot%\ee3402343t.dll���S�C(j��)������
%SystemRoot%\system32\drivers\aec.sys
%SystemRoot%\system32\drivers\AsyncMac.sys
%SystemRoot%\system32\drivers\pcidump.sys
X:\_temp.bat��X�鲡��Դ��������·����
������(chu��ng)��ע��(c��)����
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\aec
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\pcidump
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\avp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\safeboxTray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360Safebox.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360tray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\antiarp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ekrn.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RsAgent.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mfeann.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\egui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavMon.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavMonD.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavTask.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\CCenter.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RavStub.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RsTray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RsScanFrm.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AgentSvr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\QQDoctor.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\McProxy.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcshield.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rsnetsvr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\naPrdMgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpfSrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MPSVC.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MPSVC1.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KISSvc.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KPfwSvc.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\kmailmon.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KavStart.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\engineserver.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KPFW32.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KVSrvXP.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ccSetMgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ccEvtMgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\defwatch.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rtvscan.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ccapp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\vptray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcupdmgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mfevtps.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcsysmon.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcmscsvc.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcnasvc.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcagent.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\vstskmgr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\FrameworkService.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcshell.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mcinsupd.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\bdagent.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\livesrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\vsserv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\xcommsvr.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ccSvcHst.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SHSTAT.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\McTray.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\udaterui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KAVStart.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Uplive.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KWatch.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\QQDoctorRtp.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\DrUpdate.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rfwsrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\RegGuide.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MPSVC2.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MPMon.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\LiveUpdate360.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\rssafety.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\KSWebShield.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\360delays.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
���Q��RsTray
��(sh��)��(j��)��C:\WINDOWS\system32\scvhost.exe
�����h��ע��(c��)����
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\aec
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\AsyncMac
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\pcidump
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\������գ�
�����L��(w��n)�W(w��ng)�j(lu��)��
http://vv.kk***s.info:27788/qvod/host.txt
http://tj19.x9***s.com:2787/g1/tj.asp
http://xxx.fr***8888.com:26677/***.exe
