ħ��I̖ľ�R
Trojan-PSW.Win32.OLGames.fraf
���@�r�g
2010-12-09
Σ���ȼ�
��
�����Y��
ԓ�ӱ���ʹ�� "VC” ������ľ�R�������c(di��n)���ӷ���ܛ���ԄӲ��@������ "UPack” �Ӛ���ʽԇ�D��������a����,�Ӛ����L�Ȟ� "15,045” �ֹ�(ji��)��
�D��(bi��o)��" " �� ʹ�� "exe " �U(ku��)չ����ͨ�^�ļ��������W(w��ng)퓒��R�����d�����d�ȷ�ʽ�M(j��n)�Ђ�����������ҪĿ���DZIȡ�W(w��ng)�Ύ�̖���ܴa��
" �� ʹ�� "exe " �U(ku��)չ����ͨ�^�ļ��������W(w��ng)퓒��R�����d�����d�ȷ�ʽ�M(j��n)�Ђ�����������ҪĿ���DZIȡ�W(w��ng)�Ύ�̖���ܴa��
�Ñ��ж�������F(xi��n)ϵ�y(t��ng)�\(y��n)�о��������F(xi��n)��������(w��)헡�����ܛ��ʧЧ����Ҫ��Ϣ�Gʧ�ȬF(xi��n)��
��Ⱦ����
Windows 2000/Windows XP/Windows 2003/Windows Vista/ Windows 7
����;��
�ļ��������W(w��ng)퓒��R�����d�����d
������ʩ
�Ѱ��bʹ���c(di��n)���ӷ���ܛ�����Ñ����o��κ��O(sh��)�ã��c(di��n)���ӷ������Ԅӱ��o(h��)����ϵ�y(t��ng)����ԓ���������ֺ��Ɖġ��oՓ���Ƿ��ѽ�(j��ng)���������°汾���c(di��n)���ӷ������܉���Ч���ԓ������������]�Ќ��c(di��n)���ӷ���ܛ�����������°棬�c(di��n)���ӷ���ܛ���ڰl(f��)�F(xi��n)ԓ��������ʾ���l(f��)�F(xi��n)“δ֪ľ�R”��Ոֱ���x��h��̎������D1��
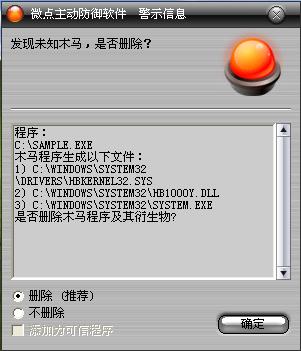
�D1 �c(di��n)���ӷ���ܛ���ԄӲ��@δ֪������δ������
������ѽ�(j��ng)���c(di��n)���ӷ���ܛ�����������°汾���c(di��n)������ʾ���l(f��)�F(xi��n)ľ�R "Trojan-PSW.Win32.OnlineGames.fraf”��Ոֱ���x��h������D2����
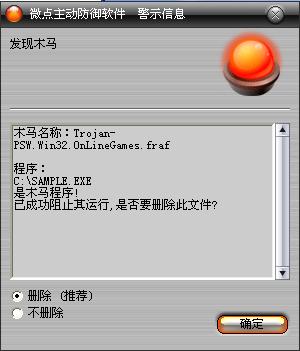
�D2 �c(di��n)���ӷ���ܛ��������ث@��֪����
δ���b�c(di��n)���ӷ���ܛ�����քӽ�Q�k����
��1���քӄh������ע�Ա�헣�
HKLM\Software\Microsoft\Windows\CurrentVersion\Run
���Q��HBService32
��(sh��)��(j��)��System.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows\
���Q��AppInit_DLLs
��(sh��)��(j��)��
HBmhly.dll,HB1000Y.dll,HBWOOOL.dll,HBXY2.dll,HBJXSJ.dll,HBSO2.dll,HBFS2.dll,HBXY3.dll,HBSHQ.dll,
HBFY.dll,HBWULIN2.dll,HBW2I.dll,HBKDXY.dll,HBWORLD2.dll,HBASKTAO.dll,HBZHUXIAN.dll,HBWOW.dll,
HBZERO.dll,HBBO.dll,HBCONQUER.dll,HBSOUL.dll,HBCHIBI.dll,HBDNF.dll,HBWARLORDS.dll,HBTL.dll,
HBPICKCHINA.dll,HBCT.dll,HBGC.dll,HBHM.dll,HBHX2.dll,HBQQHX.dll,HBTW2.dll,HBQQSG.dll,HBQQFFO.dll,
HBZT.dll,HBMIR2.dll,HBRXJH.dll,HBYY.dll,HBMXD.dll,HBSQ.dll,HBTJ.dll,HBFHZL.dll,HBWLQX.dll,HBLYFX.dll,
HBR2.dll,HBCHD.dll,HBTZ.dll,HBQQXX.dll,HBWD.dll,HBZG.dll,HBPPBL.dll,HBXMJ.dll,HBJTLQ.dll,HBQJSJ.dll
HKLM\SYSTEM\CurrentControlSet\Services\HBKernel32\
��2���h�������ļ�
%SystemRoot%\system32\HB1000Y.dll
%Temp%\HBSelfDel.dll
%SystemRoot%\system32\drivers\HBKernel32.sys
%SystemRoot%\system32\System.exe
׃������
%SystemDriver%��������������ϵ�y(t��ng)���ڷօ^(q��)��ͨ����“C:\”
%SystemRoot%����������������WINDODWS����Ŀ䛣�ͨ����“C:\Windows”
%Documents and Settings%�����Ñ��ęnĿ䛣�ͨ����“C:\Documents and Settings”
%Temp%�����������������������R�r�ļ��A��ͨ����“C:\Documents and Settings\��(d��ng)ǰ�Ñ����Q\Local Settings\Temp”
%ProgramFiles%��������������ϵ�y(t��ng)����Ĭ�J(r��n)���bĿ䛣�ͨ���飺“C:\ProgramFiles”
����������
��1����%SystemRoot%\system32Ŀ���ጷńӑB(t��i)朽ӎ�HB1000Y.dll�ͿɈ�(zh��)���ļ�System.exe����%SystemRoot%\system32\driversĿ���ጷ�HBKernel32.sys�ļ���ጷńӑB(t��i)朽ӎ�HBSelfDel.dll��%Temp%Ŀ���
��2��ע�Գ�����HBKernel32�ķ���(w��)�����Ӵ˷���(w��)�Լ��d�(q��)��HBKernel32.sys�����ڻ֏�(f��)ϵ�y(t��ng)����(w��)��һЩ��헣�ʹ��ܛ���ӷ����oЧ���ܚ�ܛ�隢
��3����������ע�Ա�헌��F(xi��n)System.exe���_�C(j��)���ӣ�
HKLM\Software\Microsoft\Windows\CurrentVersion\Run
���Q��HBService32
��(sh��)��(j��)��System.exe
��3��ľ�R�����\(y��n)��System.exe֮������HBSelfDel.dll�������з�ʽ�h���Լ���System.exe��������t������ע�Ա팍�F(xi��n)�ӑB(t��i)朽ӎ���؆����d��
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows\
���Q��AppInit_DLLs
��(sh��)��(j��)��
HBmhly.dll,HB1000Y.dll,HBWOOOL.dll,HBXY2.dll,HBJXSJ.dll,HBSO2.dll,HBFS2.dll,HBXY3.dll,
HBSHQ.dll,HBFY.dll,HBWULIN2.dll,HBW2I.dll,HBKDXY.dll,HBWORLD2.dll,HBASKTAO.dll,
HBZHUXIAN.dll,HBWOW.dll,HBZERO.dll,HBBO.dll,HBCONQUER.dll,HBSOUL.dll,HBCHIBI.dll,
HBDNF.dll,HBWARLORDS.dll,HBTL.dll,HBPICKCHINA.dll,HBCT.dll,HBGC.dll,HBHM.dll,HBHX2.dll,
HBQQHX.dll,HBTW2.dll,HBQQSG.dll,HBQQFFO.dll,HBZT.dll,HBMIR2.dll,HBRXJH.dll,HBYY.dll,HBMXD.dll,
HBSQ.dll,HBTJ.dll,HBFHZL.dll,HBWLQX.dll,HBLYFX.dll,HBR2.dll,HBCHD.dll,HBTZ.dll,HBQQXX.dll,HBWD.dll,
HBZG.dll,HBPPBL.dll,HBXMJ.dll,HBJTLQ.dll,HBQJSJ.dll
��4���ӑB(t��i)���ļ�HB1000Y.dll���b�d��(zh��)�к�ͨ�^API����(sh��)SetWindowsHookExA�O(sh��)��ȫ���^��ԇ�D������ע�뵽�����M(j��n)���У�ʹ�ú���(sh��) CreateWindowExA��(chu��ng)������qiannian���[�ش��ڣ��O(ji��n)ҕ�Ñ�ݔ����P(gu��n)�I��Ϣ�����_(li��n)�W(w��ng)���@ȡ�����Α���Ñ������ܴa�l(f��)�����ڿ�ָ���ĵ�ַ
������(chu��ng)���ļ���
%SystemRoot%\system32\HB1000Y.dll
%Temp%\HBSelfDel.dll
%SystemRoot%\system32\drivers\HBKernel32.sys
%SystemRoot%\system32\System.exe
������(chu��ng)��ע�Ա���
HKLM\Software\Microsoft\Windows\CurrentVersion\Run
���Q��HBService32
��(sh��)��(j��)��System.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows\
���Q��AppInit_DLLs
��(sh��)��(j��)��
HBmhly.dll,HB1000Y.dll,HBWOOOL.dll,HBXY2.dll,HBJXSJ.dll,HBSO2.dll,HBFS2.dll,HBXY3.dll,
HBSHQ.dll,HBFY.dll,HBWULIN2.dll,HBW2I.dll,HBKDXY.dll,HBWORLD2.dll,HBASKTAO.dll,
HBZHUXIAN.dll,HBWOW.dll,HBZERO.dll,HBBO.dll,HBCONQUER.dll,HBSOUL.dll,HBCHIBI.dll,
HBDNF.dll,HBWARLORDS.dll,HBTL.dll,HBPICKCHINA.dll,HBCT.dll,HBGC.dll,HBHM.dll,HBHX2.dll,
HBQQHX.dll,HBTW2.dll,HBQQSG.dll,HBQQFFO.dll,HBZT.dll,HBMIR2.dll,HBRXJH.dll,HBYY.dll,HBMXD.dll,
HBSQ.dll,HBTJ.dll,HBFHZL.dll,HBWLQX.dll,HBLYFX.dll,HBR2.dll,HBCHD.dll,HBTZ.dll,HBQQXX.dll,HBWD.dll,
HBZG.dll,HBPPBL.dll,HBXMJ.dll,HBJTLQ.dll,HBQJSJ.dll
HKLM\SYSTEM\CurrentControlSet\Services\HBKernel32\
���Q��DisplayName
��(sh��)��(j��)��HBKernel32 Driver
HKLM\SYSTEM\CurrentControlSet\Services\HBKernel32\
���Q��ImagePath
��(sh��)��(j��)��system32\DRIVERS\HBKernel32.sys
�����L���W(w��ng)�j(lu��):
http://www.tian***.hk.cn/q***/post.asp
http://www.tian***.hk.cn/q***/post.asp
